Data @ Rest
 Data @ Rest is an information security podcast presenting accessible, informed discussions of various topics in computer, network, and information security. If you’re curious about what to do when you receive a phishing email, the history of threat detection, or pop culture representations of the industry overall, this is the podcast for you!
Data @ Rest is an information security podcast presenting accessible, informed discussions of various topics in computer, network, and information security. If you’re curious about what to do when you receive a phishing email, the history of threat detection, or pop culture representations of the industry overall, this is the podcast for you!
Most episodes feature an expert guest, a history lesson, and a discussion of the current state of the topic.
Season Three is available now and feature topics including: cloud security operations, biometrics, network security, shadow IT, what do the different members of an information security office actually do, a whole episode about free learning resources for people interested in information security, intellectual property theft, and more.
We hope you enjoy listening!
-The Data @ Rest Team
Data @ Rest is available on Apple Podcasts, Google Podcasts, Pandora, Spotify, or other podcast apps by searching for Data at Rest.
You can also find the episodes directly on the web by streaming in your browser at our Libsyn site by visiting https://data-at-rest.libsyn.com.
What is Data@Rest: Bits n’ Bytes
A half-day virtual event focused on information security that features a variety of voices from the UNC IT community in a TED Talk style format. Some talks are long, some are short, it just depends on the topic! Our goal for this event is to create an opportunity for the IT community to get some CPE credits for certifications, share some insights about challenges we all face in the information security space, or even simply raise the profile of a project or team.
So why is Data@Rest in the title? Because it is also the release date of Season 4 of the ITS Information Security Office’s podcast Data@Rest!
When is it?
The morning of Friday, March 26th from 9am to 12 noon.
Speakers
Kim Stahl – ITS Senior Policy and Process Lead
Kim has been in the IT industry long enough to gain several credentials (MSIS, JD, PMP) and do many kinds of jobs (user support, UNIX administration, database design, CIO) but she enjoys policy the most because it has the potential to make everything else in IT more effective.
Kim will be sharing a talk titled “Why So Sensitive?: A discussion of data governance”
Dave Eiselman – Network Security Specialist
Dave will be discussing password management tools, and sharing a bit about LastPass.
Stephen Allen – Systems Programmer & Analyst
Stephen will be sharing with us about Gamification in Information Security Training.
Quinton Johnson – Export Control Officer
As the Export Controls Officer, Quinton provides expertise and personalized support to the UNC community through training and program development with the goal of reducing UNC’s overall compliance risk. Join him as he shares a bit about what that means for the larger community, and introduces us to his office.
Drew Trumbull – Information Security Incident Handler
Michael Williams and Charlie Mewshaw – Hosts of Data@Rest
In addition to hosting the event, Michael and Charlie will perform a live phishing exercise to demonstrate how easy it is implement simulated phishing campaigns for increased user awareness.
How to Sign Up
Registration is free and available for the entire UNC community at:
Enter your contact information and a link to the webinar with the passcode for entry will be sent to your UNC e-mail address the week of the event.
Meet Your Hosts
 |
Charlie Mewshaw is the Security Operations and Incident Handling team lead at UNC Chapel Hill’s Information Security Office and co-host of Data@Rest. He’s a perpetual optimist that things are getting better in the field and that people, not appliances, are at the core of strong security program. He has the CISSP, CASP, GSTRT, and GPEN certifications. He has been known to enjoy making things that kick off SCEP alerts. Some of his hobbies include video games, tabletop games, and hiking. |
 |
Michael G. Williams is the Network Security Team Lead for UNC Chapel Hill’s Information Security Office and co-host of Data@Rest. He’s been with UNC Chapel Hill for eleven years. Prior to coming to UNC, he spent a decade managing network security services for large enterprise clients in the telecomm industry. Michael has the CISSP and PCNSE certifications. In his free time he pursues any number of hobbies, including tabletop games, podcasting, and his many pets. |
| Behind the Scenes – Season 2.5 Zoomisodes | |
|---|---|
Charlie’s desk buddies…they made it from the office to the garage!  |
Charlie’s cave-like garage workspace with UNC surplus table, computer, and chair.  |
Michael’s well organized and stately remote workspace/recording space.  |
Administrative supervisor at Michael’s space.  |
Tech support at Michael’s space.  |
HR at Michael’s space.  |
| Behind the Scenes – Season 2 | |
|---|---|
Michael, Harrison, Charlie, and the TI-99/4a. 
(photo courtesy of Jessica Wynblatt) |
Trying to explain that having a face and disposition for radio doesn’t make for easy photo sessions. 
(photo courtesy of Jessica Wynblatt) |
Our new digs at the School of Medicine. 
(photo courtesy of Jessica Wynblatt) |
New digs at School of Medicine pt. 2. 
(photo courtesy of Jessica Wynblatt) |
Gearing up for the gaming episode.  |
The recorder used for live recording the gaming episode.  |
Season 2 promotional swag. Want some? Hit us up!  |
| Behind the Scenes – Season 1 | |
|---|---|
Room 1204 studio w/ cutting edge sound dampening promotional blanket. |
Michael’s Zoom iQ6 microphone.  |
Michael’s custom soundproof box. |
The heart and soul of the entire operation, the TI-99/4a with Terminal Emulator II.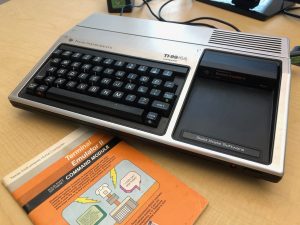 |
Boot screen for the TI, getting ready to sass its human handlers. |
Our logo, created by Isabella Gonzalez, thanks Isabella!  |
Season 1 promotional swag. |
Feel free to drop us a line at dataatrest(at)unc.edu, we’d love to hear what you think.
