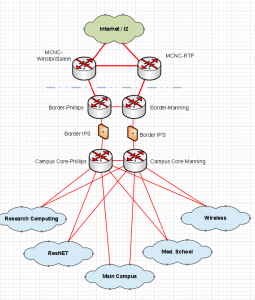
The UNC-Chapel Hill data network currently supports more than 40,000 users with over 100,000 connected devices seen on a daily basis in over 300 buildings with high-speed interconnectivity between buildings. The core routing architecture consists of a redundant infrastructure with 40 Gbps inter-switch connectivity and multiple 10 Gbps links to redundant border routers. The campus network has approximately 3,000 Ethernet switches and 10,000+ Wi-Fi access points.
Help and more information
Acceptable Use Policy Campus VPNNetworking Reports
Current:
Annual Network Report Year 2023
Past:
Biannual Report July – December 2022
Biannual Report January – June 2022
Biannual Report July – December 2021
Biannual Report January – June 2021
Data networking
UNC-Chapel Hill connects to the statewide network, NCREN (North Carolina Research and Education Network), that provides connectivity to all schools in the UNC system, all K-12 schools in the state of North Carolina, many private colleges and universities, community colleges, state government, and the North Carolina TeleHealth Network (NCTN). Through NCREN, UNC-Chapel Hill connects via IPv4 and IPv6 to Internet2 for connectivity to other universities across the country and to multiple ISPs for commodity Internet services.
The data networking staff is responsible for development, deployment, management and maintenance of data communications on the UNC-Chapel Hill campus data backbone and data communications within all University buildings. These services are of an evolving nature given the historical leading edge nature of the data network users at Carolina.
- Physical layer network infrastructure design, installation and maintenance services for Ethernet and 802.11 wireless
- Network electronics/device configuration, installation, management and maintenance services
- Network electronics firmware maintenance
- Network electronics design for intra-building
- Network electronics design for inter-building (backbone)
- Documentation of network electronics
- Proactive network benchmarking and monitoring
- Administration of internal systems required for delivery of services and network management
- Network consulting/troubleshooting for IP
- Internet and Internet2 connectivity from the UNC-Chapel Hill campus
- Connectivity to off-campus departments
- Information dissemination: Web
- On-going research and evaluation efforts, with results leading to campus network design evolution
Data networking resources
Connections to MCNC
Ryan Turner, Senior Manager / Head of Networking
r@unc.edu
919-445-0113
Network Engineering / Operations
Jerry Woodside, Manager of Network Engineering
jerry_woodside@unc.edu
919-445-0139
Robert Henderson, Jr, Senior Network Engineer
robert_henderson@unc.edu
(919) 445-8080
Frank Seesink, Senior Network Engineer
frank@unc.edu
919-445-0113
Dawn Douglass, Senior Wireless Engineer
ddouglass@unc.edu
919-445-0116
Brady Ballstadt, Senior Wireless Engineer
bballst@unc.edu
870-577-2797
Jonathan Campbell, Senior Network Engineer
jonathan.campbell@unc.edu
John Valenti, Wireless Engineer
jvalen@unc.edu
Senior Network Engineer, VACANT
Network Deployment
Reid Bradsher, Manager
reid1123@email.unc.edu
919-445-8317
Danny Stubbs, Network Analyst
danny_stubbs@unc.edu
919-445-9245
Mary Wezyk, Network Analyst
foscue@unc.edu
919-445-9430
Kevin Clayton, Network Analyst
kmclayto@email.unc.edu
919-445-1250
Will Allen, Network Analyst
wjallen@email.unc.edu
919-445-1901
Eric Maynor, Network Analyst
eric_maynor@unc.edu
919-445-9256
Chad Wade, Network Analyst
chad_wade@unc.edu
919-445-0114
Richard Vo, Network Analyst
rvo@unc.edu
919-445-8317
Network Architecture
Danny Shue, Manager and Network Architect
danny_shue@unc.edu
919-445-0121
Wireless Architect
VACANT
Will Whitaker, Network Services Architect
will.whitaker@unc.edu
919-445-1120
Chris Florio, Lead Programmer
florio@email.unc.edu
919-445-0112
Sid Stafford, Systems Engineer
sstafford@unc.edu
919-445-012
This page is not necessarily update as price fluctuations can vary rapidly. We often many more options, but these are the most commonly requested. Please submit a service request for an exact quote.
reviewed January 2021
| FIXED RATE PRICES FOR NETWORKING EQUIPMENT BILLCODE | DESCRIPTION | AMOUNT | |
| NETUPS WITH LINECARD | SINGLE UPS | $1,778 + labor | |
| WAP (Wifi 6) | REPLACEMENT OF EXISTING INDOOR WIRELESS ACCESS POINT | $675 + labor | |
| EXTREME 5520 48 PORT 25 GIG | 48-PORT GIG SWITCH NETWORK SERVICE | $8,504.50 | |
| EXTREME 5520 48 PORT 10 GIG | 48-PORT GIG SWITCH WITH 802.3bt PoE | $7,875 + labor | |
| EXTREME 695 BES | 48-PORT 10/25/40/50 GIG SWITCH | $15,991 + labor | |
| NETWORK DEPLOYMENT LABOR RATE (PER HOUR) | $70.00 | ||
Normal changes require CAB approval and are not discussed here. These are changes that we have defined as either Standard or Operational. Standard changes are done between 5AM and 7AM on Tuesday through Thursday and have been pre-approved with 3 days of notice. Operational changes are done at any time with no notice and are not expected to have significant client impact. All of these are subject to change with no notice. We have attempted to create an exhaustive list, but not everything we do will be listed here.
STANDARD CHANGE EXAMPLES:
- Life cycle equipment in building (coordination expected with building occupants)
- Upgrading firmware on wireless controllers
- Rebooting more than 3 APs concurrently unless the reboot is to apply a customer requested change and has no service impact
- Migration of wireless services to new hardware
- Rebooting BES switch
- Rebooting a DC switch in a redundant pair (edge or spine)
- Upgrading hostscan package on Cisco 4150 ASAs
- Upgrading AnyConnect client packages on Cisco 4150 ASAs
OPERATIONAL CHANGE EXAMPLES:
- Rebooting an AP (single action)
- Rebooting an edge switch (single action)
- Making configuration changes to wireless controllers that are not expected to interrupt service
- Changing/adding/removing a VLAN to a switch or port
- Creating a VLAN
- Changing a DHCP scope
- Creating a new network
- Router ACL configuration changes
- BGP/OSPF change for new or non-production neighbor/peer
- Changing permissions in InfoBlox
- Making changes or firmware upgrades on network monitoring systems
- Adding a new VPN group to the Cisco 4150 ASAs (AnyConnect remote access)
- Expanding a VPN group IP prefix (i.e., giving a group more IPs to use) on Cisco 4150 ASAs
- Adding an SSL certificate to an F5
- Hypervisor updates to standalone ESXi servers supporting Infoblox appliances
- Switch policy changes including assigning and enforcing switches to policy domains and making port policy changes
- Updates to NAC rules and end systems groups
- Manually Synching an F5 Load-Balancing Pair
- Server Reboots
- Service restarts or appliance reboots of individual Infoblox appliances
- A10 webproxy configuration updates for source and destination policies
- FreeRADIUS configuration updates for clients, users, and user attributes
- Upgrades or config updates to pfSense virtual appliances supporting wireless onboarding
- Updates to the active SecureW2 network profile for wireless onboarding
