October is Cybersecurity Awareness Month. In this guest post, Drew Trumbull, Incident Response Team Lead with the Information Security Office, shares how malicious actors find ways around strong security measures. All month long, ITS News will highlight this year’s theme: See yourself in cyber. In this article, seeing yourself in cyber means understanding your role in cybersecurity and how you play a critical part of keeping yourself and the University safe.

Multifactor authentication, or MFA, is widely used to help prevent malicious actors from gaining access to your accounts. Multifactor authentication also goes by names like 2-Step Verification or two-factor authentication. UNC-Chapel Hill uses two 2-Step services, Microsoft and Duo Security, to protect accounts and data at the University.
MFA means that more than one authentication method, or factor, is required to allow you access to an account. An example would be requiring both a password as your first factor and a code you receive via text as your second factor.
Requiring more than just a password increases security by making it more difficult for attackers to gain access to your account. Even if they know your username and password, they still need a second factor to get in.
Not quite perfect
Multifactor authentication provides a high level of security, but phishers, scammers and other malicious actors are highly motivated to find ways around this protection so they can steal valuable data. Hackers use techniques called MFA bypass to defeat MFA. These attacks vary in sophistication but have a few common components.
Here is a typical example:
- User receives a phishing email or text with a button or link. Sometimes this will come as a shared file from a source like Google Drive. In those cases, the user will go to a Google Drive document that contains another link.
- The link takes the user to a fake sign-in page that looks nearly identical to a legitimate site, such as the office.unc.edu login page.
- The user enters the user’s real username and password on the fake site.
- The attacker harvests the login information from the fake site and then attempts to log in to the real system using the stolen username and password.
- Prompted by the attacker’s log-in attempt at the real site, the user receives a legitimate MFA authentication (a push notification, phone call, text message, etc.) asking the user to verify the user’s identity.
- User verifies the login using the user’s MFA method, allowing the attacker into the real system.
When users have push notifications or phone call verification set as their MFA preference, these attacks are more likely to succeed. This is because the user doesn’t need to interact with the web browser by entering a code received by text or generated by an app.
MFA bypass via proxy attacks
The most advanced attackers have found a way around the limitations of interacting with the web browser by creating proxy websites. This means that attackers create a website that sits between you and the site you’re trying to connect to.
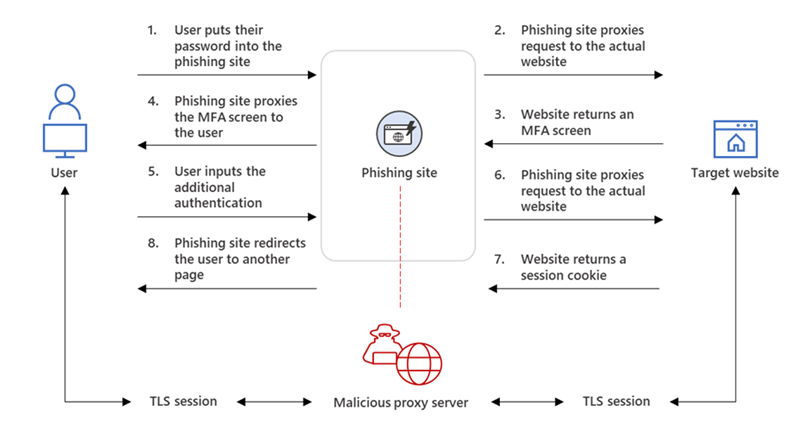
In a proxy attack, the phishing site sits between the user and the target website. The phishing site passes relevant web pages and data, including passwords and multifactor authentication, back and forth between the user and the target site.
This allows the attackers to bypass most available methods of MFA, since the user is providing the site, and the hacker, with both the username and password and additional authentication.
Protect yourself
Even with sophisticated MFA bypass techniques like proxy attacks, you can protect yourself. Here are a few tips that can help prevent you from becoming a victim:
Be suspicious
When you receive an unexpected message, from Google or any other file-sharing service such as Dropbox or Yahoo, use caution.
If you know the person or entity, contact them, through a method other than the email address the message appears to come from, to confirm the message is legitimate. If you don’t recognize the sender, do not click on any links or download any attachments.
Don’t log in again
If you are already logged into a resource, such as Microsoft 365, and are being prompted to log in to it again, that’s a red flag that the site you are visiting may not be legitimate.
Check the URL
Even in the case of a proxy attack, the link to the phishing webpage and in the URL bar once you’ve clicked it will be different than the normal address you would see when logging in.
Take note of the URL of sign-in pages you use frequently. Always double check before clicking a link in an email and after arriving on your designation page. Remember that it is always safest to type a URL into an address bar instead of following a link.
Get help
It’s important to remember that while MFA is a valuable control in preventing account compromises, it’s not a perfect solution. Unfortunately, humans are the weakest link, so remain vigilant. If you’re unsure of a situation, contact the ITS Service Desk at help.unc.edu or 919-962-HELP (4357) for assistance.
If you suspect a message is phishing, use the Report Phishing button in your email to help prevent others from becoming victims.
For more tips about phishing, visit safecomputing.unc.edu.
