
UNC-Chapel Hill is switching to a system of changing Onyen passwords to once a year rather than every 91 days. For the convenience of changing their password just one time per year, campus community members will need to create passwords that are harder for criminals to crack.
In a guest post, Alex Everett, IT Security Architect with the Information Security Office within ITS, discusses the change from an IT security perspective. He explains what makes this new system safer while also being more user friendly.
Beginning on May 13, ITS Identity Management will release a major update to the Onyen service. The update will allow constituents to use the same password for up to one year while removing all character requirements that are in place today.
We believe this will not only make for a better user experience, but also for a modestly stronger set of passwords as the service is now more closely aligned with recommendations from both the National Institute of Standards and Technology and from our very own Department of Computer Science. However, 2-Step or two-factor must continue to be a key component of authentication at the University as it protects against our greatest threat to passwords — phishing.
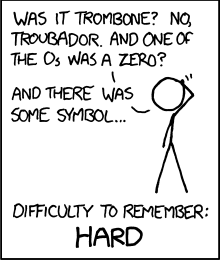
For a long-time, we have asked our constituents to memorize passwords that contain numbers, special characters and letters rather than allowing for combinations of words, phrases or sentences that are as strong and much more memorable. An excerpt from a popular comic tries to capture this.
Safer authentication technologies
We have also placed more responsibility for password strength on the constituent rather than on limiting password guessing attacks and securing password databases. However, over the past few years our colleagues in ITS Infrastructure & Operations have made progress on these fronts, including completing a risk assessment and adopting safer authenticating technologies. As such, our primary risks to Onyen passwords are from phishing attacks and to a lesser degree from online guessing attacks, especially those using compromised credentials found in external password breaches. It is important to refrain from using your Onyen password for non-University accounts, such as social media and banking. Password managers such as LastPass present a simple way to manage a multitude of credentials safely.
A preview of what to expect
This is an example of what constituents will see when they change their password beginning in May. We encourage you to set a “very strong” password.
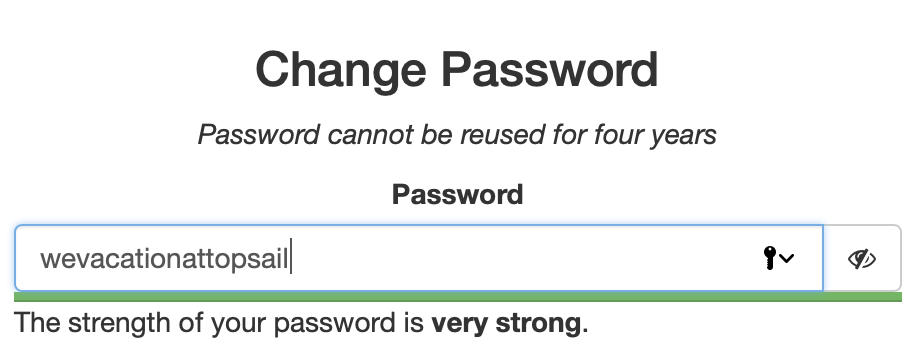
As the password is typed, the service evaluates the number of guesses an attacker must make. This service is based on an algorithm designed by Daniel Wheeler of Dropbox that attempts to mimic how attackers operate.
Rather than estimate complexity based solely on length and character sets, it estimates complexity based on a myriad of factors, including keyboard layout, repetition, frequency of words in languages, character substitutions and brute force. As such, it recognizes “C@rol1n@” to be a simple substitution of a common word and scores it as much more guessable than “redandcold,” a simple combination of three words that the service allows. This seems a little counterintuitive, but even these short passwords are as strong as many of the passwords that our constituents use today.
The service will also check the submitted password against a list of known exposed passwords from public password breaches. Additionally, it will require the new password to significantly differ from the makeup of the prior password.
Needs vary by the application
Lastly, I do want to note that a “strong” or “very strong” password allowed by the Onyen service may not be strong enough to use in other contexts. For example, if you encrypt a file and place it on a storage system that anyone at the University can access, that file can be copied and cracked offline without any limits. This is also similar to a local password on a computer server that allows thousands of (SSH, RDP or web) logins an hour without any rate-limits or monitoring. For these uses and also for service accounts, we recommend a long password that is 17 characters in length or greater as per the recently revised Passwords, Pass-phrases and Other Authentication Methods Standard.
